What Is DNS Hijacking? (Your Guide to How to Stop DNS Hijacking)
DNS hijacking has become a favorite tool of cybercriminals lately, so learning how to protect yourself from it can mean the difference between staying safe on the web or losing all your personal and financial data.
“Wait, what is DNS hijacking?”
If you’re not familiar with it, don’t worry. We’ll cover everything you need to know about it, including how to stop DNS hijacking in this article.
Table of contents
To truly understand what is DNS hijacking and how to stop DNS hijacking, you should first get a basic understanding of DNS (Domain Name System).
What Is DNS?
Basically, DNS is a protocol that makes it possible for web-connected devices to connect to and communicate with websites. It runs on various servers, and a DNS server is responsible for returning a website’s IP address when you device sends connection requests its way.
Why does it do that? Because when you enter a website’s name into your browser, your device needs its IP address to establish a connection, and it gets that info from DNS servers that contain databases of IP addresses and their associated domain names.
Here’s a quick overview of how the process works:
- You type in a website’s address in the URL bar (like “google.com”).
- Your device will send a query to a DNS server asking what Google.com’s IP address is.
- The DNS server tells your device what the IP address is.
- Your device uses that IP address to connect to Google’s website.
All that happens in the background, of course. It’s a very fast process, and you won’t notice it.
What Is DNS Hijacking?
DNS hijacking is when a cybercriminal hijacks a user’s DNS traffic. Generally, a rogue or compromised DNS server will be used to return fake IP addresses when a user’s device asks for a specific website’s address.
For example, if you try to access paypal.com, the rogue DNS server will return the IP address for a fake website like paypai.com. So, your device will unknowingly connect to a malicious website because it thinks that’s the correct IP address for paypal.com.
DNS hijacking can often take place because the DNS protocol is based on the idea that every DNS server is trustworthy. It’s easy to see how a hacker can take advantage of that with malware or compromised DNS servers.
What Is DNS Hijacking Used for?
DNS hijacking can be used in phishing and pharming attacks with the intent to steal personal and financial information from online users.
The goals are pretty obvious from there on – to empty victims’ bank account, use their credit cards in credit card fraud schemes, and sell their personally identifiable information (physical address, email address, full name, mobile number, etc.) on the deep web, or use it in other scams later on.
How Does DNS Hijacking Work?
Like we already mentioned, DNS hijacking redirects IP query results, so that your device connects to the wrong website. But let’s take a look at how most cybercriminals manage to perform DNS hijacking:
Through Malware
Malware attacks can infect your router, and change its DNS settings so that it uses hacker-owned DNS servers instead of legit ones. That way, you’re automatically redirected to any website the server owner wants.
One of the best examples of this was the DNSChanger malware. It changed router DNS settings to force online users to visit websites where cybercriminals displayed dozens of ads. Luckily, none of those ads were malicious since they were only used to drive advertising revenue.
Something much worse can happen if a hacker uses such malware to infect your router, though. You could be redirected to a malicious website that monitors your keystrokes, traffic, or installs adware, spyware, or keyloggers on your device.
Interacting with malicious ads, links, and downloads can often result in your device and your router being infected.
By Compromising DNS Servers
Hacking DNS servers is pretty complicated, but a skilled cybercriminal can pull it off. When they break through the server’s security, they just alter some of the IP addresses in the database, and wait for unsuspecting online users to be redirected to the wrong websites.
Sometimes, hackers might even be able to compromise ISP DNS servers. If that happens, all the ISP’s users will be at risk of having their personal and financial info stolen.
By Setting Up Rogue DNS Servers
Cybercriminals can set up their own DNS servers if they want. They just alter the databases on those servers, so that the wrong IP addresses are returned when they are queried.
Rogue DNS servers are often used alongside router malware attacks. However, the owners can also try to use advertising and phishing messages to get people to use them.
What Is ISP DNS Hijacking?
ISP providers can also perform a type of DNS hijacking, though it’s not as dangerous to online users as regular DNS hijacking. Still, it can be pretty annoying.
Why? Because they use it to expose you to ads in order to drive more revenue. Basically, they hijack the NXDOMAIN response – the response for non-existent Internet domains. Normally, if you type in a website address that doesn’t exist, you’d get the NXDOMAIN response which tells you exactly that.
If an ISP uses DNS hijacking, you wouldn’t get the NXDOMAIN response. Instead, you’d be redirected to a fake website that contains dozens of ads. Sometimes, the ISP might even collect user data from people who interact with ads, and sell it to third-party advertisers.
Normally, ISP DNS hijacking shouldn’t be a huge concern for you. You’d only be exposed to the fake websites if you intentionally access a non-existent website address. Though, there might be serious risks if the ads contain malware, and you access the website by mistake (mistyping the address you wanted to normally connect to).
How to Diagnose DNS Hijacking
Diagnosing DNS hijacking isn’t very simple since there is no “Yes or No” DNS hijacking test you can run. And if you’re not paying enough attention to the website you land on, you might not even realize it’s the wrong one or a fake one.
The best way to spot DNS hijacking is to make sure you’re always on the right website. If you notice any misspellings in the URL address, a lack of a website security certificate, and that no HTTPS encryption is used, you might have ended up on a phishing website.
Luckily, besides that, there are some online tools you can use to get a clearer verdict. For starters, WhoIsMyDNS.com is a website you can use to check what the actual server that made the requests on your behalf is, and if it’s a legit one or not. It will tell you if the server is on a suspicious DNS server list, who the IP owner is, and what the Reverse DNS is.
There’s also Router Checker from F-Secure Labs – a tool that verifies your device’s connection to its DNS resolver, and checks that it’s connected to an authorized DNS server. If any mismatches are reported, you’re likely the victim of DNS hijacking.
How to Stop DNS Hijacking
Learning how to prevent DNS hijacking isn’t too difficult. Just make sure you follow these tips:
1. Secure Your Router
The best thing you can do to protect your router from DNS hijacking is to change its default username and password – the ones it comes equipped with when the manufacturer ships it out. Usually, the login credentials are something along the lines of “admin/password” or so.
The problem with that is that not only are the login credentials easy to guess, but anyone can just google your router’s PDF manual, and find the default login credentials right there. With such info, they can easily take control of your router.
Outfitting your with antivirus/antimalware protection is also a good idea since it will prevent malicious attacks.
If you want to learn more about protecting your router and your home network, we’ve got an article on that topic you might be interested in.
2. Don’t Interact With Shady Websites
If you end up being redirected to a malicious website, it’s best to close your browser, shut off your device, or disable your Internet access. If you accidentally interact with anything on the website, your device and private data will likely be compromised.
To make sure you’ll be safe before you take any of the measures we mentioned above, don’t do any of the following:
- Type in any private information, usernames, or passwords.
- Click on any videos.
- Click on any pop-up messages or ads you might see.
- Hit “X” to close pop-up messages and ads. Doing that can trigger a malware infection.
How can you tell if a website is malicious or fake? It’s normally enough to check if its URL starts with “http” since a secure website address starts with “https.” Also, check if there is a green padlock icon before or after the URL address. Normally, you should be able to click on it to find out more details about the website’s security certificate – a certificate that can confirm that the website owner’s identity has been verified.
Flashy, aggressive ads and CTA buttons are also red flags.
3. Use a VPN Service
A VPN (Virtual Private Network) is an online service that can hide your IP address, and encrypt your online traffic. And online traffic includes your DNS traffic as well, so a VPN can prevent cybercriminals from trying to monitor it so that they can target you with DNS hijacking attacks.
So, you should always use a VPN when accessing the web – especially since it can keep you safe even on unsecured public WiFi. What’s more, you can configure VPN connections on your home router too, so that your entire network traffic is secured.
Protect Yourself From DNS Hijacking With CactusVPN
Our high-end solution can make sure your DNS traffic is never exposed on the web by securing it with military-grade encryption and state-of-the-art protocols like SoftEther, OpenVPN, IKEv2, and SSTP.
Plus, we also offer a Kill Switch to make sure you’re always safe – even if your VPN connection happens to go down. That, and our service comes equipped with DNS leak protection as well.
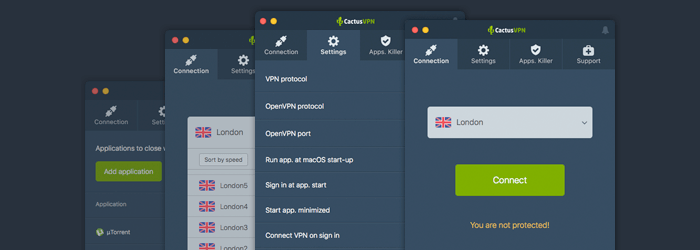
Special Deal! Get CactusVPN for $3.5/mo!
And once you do become a CactusVPN customer, we’ll still have your back with a 30-day money-back guarantee.
4. Don’t Rely on Public WiFi
Using public WiFi to browse the web is usually risky because it’s often unencrypted, meaning anyone can see your traffic (including your DNS traffic) if they want to. Plus, you don’t know what DNS server the public WiFi network uses. If they are compromised or rogue servers, you’ll automatically be a victim of DNS hijacking.
Ideally, you should try using your data plan instead. Or just make sure you have your VPN running since your traffic will be safe then at least. There are also other things you can do to keep yourself safe on public WiFi.
5. Consider Using a Different DNS Server
By default, you will be using your ISP’s DNS server when browsing the web. That’s not necessarily a bad thing, but there’s always a risk that cybercriminals could compromise it. If that happens, all your connection requests that are routed through your ISP’s DNS server will be redirected to malicious websites.
Ideally, you should consider using third-party options like OpenDNS and Google DNS. They offer decent security, and are free to use (except some of OpenDNS’ most high-end plans). Alternatively, you could use a reliable Smart DNS provider as well. In fact, to get the best results, you should consider using a VPN provider who also offers access to a either a Smart DNS service or a DNS server.
Just don’t use a DNS server that comes from a shady source – namely somebody you don’t know anything about. Giving a stranger control over your DNS traffic won’t do you any favors.
Lastly, consider this – if you don’t use your default ISP DNS server, you should normally be safe from ISP DNS hijacking. If you somehow still experience it, try following this fix.
6. Use Strong Antivirus/Antimalware Protection
Antivirus/Antimalware software won’t provide a direct DNS hijacking fix, but it can help protect your devices from malware and virus infections. Plus, some programs can warn you when you’re accessing a malicious website, or just block harmful downloads or links from opening.
Also, make sure you keep the software up-to-date at all times. If you don’t, it might miss a valuable update that could help it combat the latest malware threats.
There are plenty of antivirus/antimalware software providers to choose from, but our recommendations are Malwarebytes and ESET.
7. Use DNSSEC (Domain Name System Security Extensions)
If you’re not familiar with DNSSEC, it’s an industry-wide security standard that boosts DNS security by outfitting the protocol with:
- Data origin authentication to ensure that the DNS resolver (the tool responsible for resolving an user connection requests) actually “knows” for certain that the data it received came from the right place.
- Data integrity protection, which makes sure that the DNS resolver can see if the data that’s in transit has been tampered with or not.
Before you start looking up how-to articles on DNSSEC, you should know that it’s not the kind of thing anyone can implement. You need to meet the following requirements:
- You need to be connected to or run a home/business network.
- You need to have access to the DNS resolver.
- The DNS resolver must be able to support DNSSEC.
Before we discuss that, you should use this link to see if DNSSEC isn’t already installed and working on your network. Basically, just access the websites that have a bad DNSSEC signature. If you’re able to do it, it means there’s no DNSSEC enabled.
Now, how do you find out if you can tweak your DNS resolver settings? Luckily, it’s not that hard. Just use this tool on one of the devices on your network. It will offer you the IP address of your network’s DNS resolver. If the address is in the same range as your computer’s IP address, that most likely means your router is the DNS resolver.
In that case, just access your router’s admin console, and look for an option that lets you enable DNSSEC. If there is no such option, your router probably doesn’t support DNSSEC. If that happens, you can try browsing the manufacturer’s website or contacting the manufacturer to find out if there’s a way to enable DNSSEC through a patch. If there isn’t, the only thing you can do is get a router that offers support for DNSSEC.
“What if the IP address given to me by that tool isn’t in the same address range as my computer’s IP address?”
That most likely means that the DNS resolver is operated by your ISP. Unfortunately, there’s not much you can do in that case other than trying to contact your ISP, find out why they are not using DNSSEC, and if they are willing to use it. The only other option is looking for a better ISP.
8. Use Script Blockers and Anti-Phishing Extensions on Your Browsers
If you ever get redirected to malicious websites because of DNS hijacking, it helps to have an extra layer of security even if you don’t plan on interacting with the malware-infected platforms.
For starters, script blockers are invaluable because they can prevent malicious background scripts from starting up when you land on a hacker’s website. For example, a script blocker can prevent crypto-mining scripts from harming your device, or malicious pop-up ads or videos from displaying.
Right now, the best script blockers to use include uMatrix and uBlock Origin.
Besides them, you should also use anti-phishing extensions – like the ones Stanford offers. They are a great way to prevent context-aware phishing attacks, and to make sure you are warned when you land on a phishing page.
What Is DNS Hijacking? The Bottom Line
So what is DNS hijacking? Well, it’s when cybercriminals manage to compromise your DNS traffic or the DNS server your device uses when sending connection requests to websites. Basically, they change the IP addresses that should normally be returned, so that you are redirected to fake and malicious websites.
Cybercriminals usually perform DNS hijacking by exploiting ISP DNS server vulnerabilities, setting up their own DNS servers, or exposing routers to malware infections that alter DNS settings.
It should be noted that ISPs can also perform DNS hijacking, but they normally do it to redirect users from websites that don’t exist to fake websites that contain dozens of ads. Why? To make ad-based revenue, basically.
How do you know if you’re a victim of DNS hijacking? Well, it can be hard to tell, but if you end up on a shady website when accessing a legit one, that’s a dead giveaway. You can also use Router Checker and WhoIsMyDNS.com to get some more accurate results.
“Can I learn how to stop DNS hijacking?”
Yes, there are some things you can do, like:
- Using reliable antivirus/antimalware solutions.
- Using a decent VPN service.
- Installing script blockers and anti-phishing ads on your browsers.
- Not interacting with any website elements if you do end up getting redirected to a fake one.
- Using DNSSEC on your home or business network.
- Changing DNS servers.
- Not using public WiFi (or using it while running a VPN connection at least).
- Changing the default username and password on your router, and securing it with antivirus/antimalware.
 Tips on How to Use a Public Computer Safely
Tips on How to Use a Public Computer Safely
 How you’re being manipulated online – quick guide to online manipulation
How you’re being manipulated online – quick guide to online manipulation 