Is Tor Safe for Online Browsing? (Not Really – Here’s Why)
With nearly two million people using it, the Tor network is one of the most popular ways to anonymize your online browsing right now.
But you got to wonder – is Tor safe, actually?
It makes a lot of promises, after all – online anonymity, complete privacy, secure encryption, unrestricted access, and so on.
To make a long story short, no, Tor really isn’t too safe to use on the web if you want great privacy and security.
Of course, things aren’t as simple as a basic “no.” So, let’s take a look at Tor – how it works, why it isn’t as safe as it claims to be, what other inconveniences you need to deal with, and what you can do to make it more secure overall.
First Things First – What Is Tor & How Does It Work?
Tor stands for The Onion Router. It’s an anonymity network (at least that’s how it calls itself) that’s run by volunteers.
To access the network, you need to use the Tor browser, which is both free and open-source.
As for how it works, it’s pretty simple – when you connect to the network, it routes your traffic through different servers (called relays). Usually, your traffic will go through at least three servers: the entry node, middle node, and exit node.
The network encrypts your traffic multiple times. Each time it hits a node, it losses a layer of encryption. Once it reaches the exit node, it’s completely decrypted and forwarded to the web.
Besides encrypting your traffic, Tor will also hide your IP address, replacing it with the address of its servers. The website you access will only see the IP address of the exit node.
Is Tor Illegal?
To put it simply, no. The Tor devs make it clear that “Tor is not illegal anywhere in the world.”
While we didn’t find any specific laws regarding Tor, you should keep in mind that laws are usually vague when it comes to stuff like this. So, it might be possible to assume that countries that ban or make VPNs illegal have the same stance on Tor.
Of course, if you ever use Tor to access illegal content (child pornography, drug trades, contract killer websites), you can get in serious trouble with the law.
But not all the content on the deep web is of that nature. In fact, according to data, around 55% of it is legal.
All in all, you don’t need to worry about legal repercussions if you only use Tor to access legal content on the deep web, hide your IP address, and encrypt your traffic – unless your country has laws that prevent that kind of activity.
Is Tor Safe? Here Are 8 Reasons Why the Answer Is a Clear “No”
Here’s exactly why you shouldn’t use Tor if you want a safe and private online browsing experience:
1. Tor Has Issues With Malicious Nodes
Security researchers actually found at least 110 Tor nodes that were snooping on user traffic and exposing devices to malware. In fact, one exit node was configured to alter any files users downloaded through it with malicious executable code that turned said files into rootkits, basically giving hackers remote control over the victim’s device.
And the 110 nodes were discovered over a period of just 72 days. Who knows how many are actually out there.
Here’s the thing about Tor nodes – pretty much anyone can set up and operate them. It’s part of Tor being a decentralized network.
That has its advantages, obviously – it’s what gives Tor the feeling of anonymity in the first place.
However, the main problem with decentralization is that any cybercriminal can set up a Tor node if they want to. Here’s just one example out of many – back in 2007, a Swedish hacker set up multiple Tor nodes. Over the course of a few months, he collected sensitive data – specifically login credentials for around 1,000 accounts.
Actually, you know what – here’s another even better example of that: WikiLeaks. That’s exactly how it got its start – by using Tor nodes to log tons of private documents.
We’re not saying WikiLeaks is a bad thing, but it does show that anyone can get their hands on sensitive information with Tor nodes like they did.
Obviously, that includes government agencies too. Tor devs themselves made it public that government officials seized control of Tor servers through Operation Onymous.
2. Tor Traffic Makes You Really Stand Out
Even though Tor traffic is designed to imitate HTTPS, network admins can still tell if you’re using the network.
It’s not exactly clear how someone can tell you’re using Tor, but here’s an example of that – a student using Tor to send bomb threats through email.
We’re not gonna debate what he did (obviously, it was wrong). Instead, we’ll focus on the criminal complaint. According to it, the university was actually able to see that the student in question accessed Tor with their WiFi network a few hours before the threats were received.
That might be because Tor has serious vulnerabilities or ties to the government (we’ll get to that in a bit). However, it might also be due to the fact that there are services (like Plixer and CapLoader) that make it possible to separate Tor traffic from normal HTTPS traffic.
Plus, here’s another problem with Tor – most people say it’s very useful for people who live under oppressive regimes since it hides their online activities. Well, the main issue with that is those regimes will be specifically targeting Tor traffic.
So, you won’t be very incognito. In reality, you’ll stand out like a sore thumb.
3. The Government Has Many Ways to Compromise the Network
As strong as Tor encryption might be, it can’t stand against government interference. Security researchers actually worked for the federal government to find a way to break Tor.
Not only that, but apparently the NSA also figured out ways to de-anonymize Tor users on a “wide scale.”
And back in 2015, security researchers found a way to unmask Tor users by using hardware that only costs $3,000. True, they did that for a noble cause (busting pedophiles and drug dealers), but that doesn’t change the fact that government agencies can use similar techniques to target innocent users too.
Oh, and back in 2014, there were even attacks against the Tor network that allowed the NSA (and any other agency, really) to de-anonymize around 81% of Tor users.
Most recently, the FBI apparently managed to de-anonymize Tor users to the point of finding their real IP addresses. The weird thing is that they decided to drop the case against child pronographers (which resulted in them walking free) so that they don’t disclose the Tor vulnerability they abused.
4. Exit Nodes Don’t Really Encrypt Your Traffic
Tor bounces your traffic between multiple servers, decrypting a small layer of encryption with each bounce (hence the “Onion” in The Onion Router name).
Well, when your traffic passes through the last server, there’s no more encryption.
Now, that normally would make sense since VPNs work the same way – the server decrypts the traffic to forward it to the web.
But unlike a VPN, anyone can set up a Tor node like we already mentioned. And according to Tor documentation, the exit node can actually see the contents of your message.
If a hacker or government agency is running that exit node, that pretty much means they’ll see what you’re doing on the web.
With VPNs, that’s normally not a problem since they control their own servers, and generally rent them from reliable data centers. Plus, good VPNs don’t log any of the data that passes through the server.
What’s more, according to an experiment from a security researcher, a large number of exit nodes sniff the data they decrypt.
5. Tor Devs Actually Cooperate With the US Government
Even though the Tor Project portrays itself as being anti-Big Brother and caring about the little guy, a journalist used FOIA (Freedom of Information Act) requests to tell a different story.
Basically, it seems that one of Tor’s co-founders (Roger Dingledine) had no problem discussing cooperation with the DOJ and FBI. Oh, and he also referenced installing “backdoors.”
Another exchange showed that a dev found a vulnerability that would essentially de-anonymize Tor users. The dev suggested keeping the vulnerability an internal matter, yet Roger Dindgledine went ahead and told government agents about the vulnerability after just two days.
If you’d like to read more about the exchanges (we highly recommend it), check out this link.
6. Tor Receives Funding from the US Government
If the ties weren’t enough, then the fact that the US government invests money into Tor should convince you that there’s no way the network can 100% protect your privacy.
Here is how much money Tor got from the US government:
- $2.2 million from the Pentagon.
- $6.1 million from the BBG (Broadcasting Board of Governors) – now known as USAGM (U.S. Agency of Global Media). Basically, this is a spin-off CIA agency.
- $3.3 million from the State Department.
And get this – the Tor devs themselves said that investors actually get to influence the direction of the project’s research and development.
Oh yeah, that doesn’t look shady at all.
Let’s be real for a moment – do you really think the US government would siphon so much money into a network that can allegedly ruin their surveillance plans?
Yeah, didn’t think so either.
In fact, it’s safe to say that the US government is the one who created Tor. If you listen to this speech from Roger Dingledine, you’ll hear him clearly say that:
“I contract for the United States Government to build anonymity technology for them and deploy it.”
“They need these technologies so that they can research people they’re interested in, so that they can have anonymous tip lines, so that they can buy things from people without other countries figuring out what they are buying, how much they are buying and where it is going, that sort of thing.”
Roger Dingledine
Actually, just google “Tor history,” and you’ll see it got its start in the United States Naval Research Laboratory – a branch of the US Navy.
And in the same speech, you can hear Roger Dingledine say the following:
“The United States government can’t simply run an anonymity system for everybody and then use it themselves only. Because then every time a connection came from it people would say, “Oh, it’s another CIA agent looking at my website,” if those are the only people using the network. So you need to have other people using the network so they blend together.”
Roger Dingledine
If it’s not clear enough, when you use the Tor network, you’re pretty much helping CIA agents who are using it conceal themselves.
Considering all that, is it really surprising that the answer to “is Tor safe?” will always be a resounding “no”?
Don’t worry, though – if you’re not 100% convinced yet, we’ve still got two more reasons why Tor isn’t safe to go through.
7. Tor Can Leak IP Addresses
Back in 2017, the Tor network had a serious flaw called TorMoil that leaked users’ IP addresses. While the devs eventually fixed that problem, there’s no telling when it will occur again.
What’s more, Tor can actually leak your IP address in other instances if you don’t use the Tor browser exclusively:
- When you try to open Windows DRM files. Apparently, that can decloak Tor traffic, revealing your IP address.
- When you download torrents since many clients will leak your IP address.
- If you try to access certain types of files (like PDFs), they will bypass proxy settings, resulting in a leaked IP address.
Those problems don’t always happen due to Tor, though. It’s often because Tor users misconfigure settings.
Of course, that doesn’t make things better. It just means you have extra hassle to deal with when using Tor.
Also, when you consider how many ties the Tor Project has with the US government, it’s hard not to wonder just how “accidental” those IP leaks really are.
8. Government Agencies Don’t Even Need Warrants to Spy on Tor Users
The FBI and US District Court made it pretty clear – it doesn’t matter what you do on the Tor network. If the FBI wants to, they can spy on you without needing any warrants.
True, this ruling came into effect after the FBI shut down a child pornography ring, which is definitely a good thing.
But (and it’s a big “but”), that does mean the FBI can now treat anyone who uses Tor as a criminal if they want to – even if you’re just using the network to hide your IP address and nothing more.
Also, check this out – according to this official document from a case, a judge ruled that Tor users don’t actually have “a reasonable expectation of privacy.”
So yeah, according to the law (at least in the US), if you decide to use Tor to protect your privacy, you should actually expect government agencies to start spying on you.
Other Reasons Why Tor Isn’t Such a Great Option
So, is Tor browser safe to use?
We pretty much established that no.
But besides that, there are other reasons you shouldn’t use it to browse the web:
The Speeds Are Pretty Bad
Remember how we said there are almost two million Tor users?
Well, there are only around 6,000 servers to support them. Simply not enough to go around, so Tor users end up quickly overloading the network.
Plus, Tor bounces your traffic between multiple servers, which further contributes to the slow speeds.
And this isn’t some secret. If you google “Tor slow,” you’ll find dozens of people complaining about that.
Also, you’ll see that the Tor devs themselves clearly state the network is slow. While they do offer some tips on how to speed up your connections, you won’t really notice a huge difference.
It’s Really Not Good for Torrenting
Besides the fact that Tor can leak your IP address when you download torrents, there is another reason you can’t really use it for that – because the devs didn’t design it for torrenting.
The speeds are pretty slow, so you won’t get decent download and upload speeds.
That, and the Tor devs themselves say using the Bittorrent protocol over Tor is not a good idea.
In fact, if you head to the downloads page on the Tor website, you’ll see a Warning section. The first thing you’ll read there is “Please do not torrent over Tor.”
Governments Can Actually Block the Tor Network
Even if you were to ignore Tor’s security flaws, you still wouldn’t be able to enjoy a stable experience.
Why?
Because your government might suddenly decide to block access to the Tor network – like Venezuela, China, and Turkey already did.
In fact, even your ISP can block direct use of Tor if they want to.
And here’s the kicker – it’s not even hard for an ISP or government to do that.
Really, all they have to do is check the current list of Tor nodes, and use routers and firewalls to block them.
Tor Can’t Access Many Websites
Specifically websites that use Cloudflare security software since it has a firewall option that blocks Tor traffic.
Unfortunately, a lot of websites use Cloudflare. It’s hard to tell exactly how many, though these statistics claim that around 10.5% of the total number of websites (around 1.5 billion) use Cloudflare. So, that’d be around 157 million websites.
Some examples of those websites include 9gag, PCMag, Medium, Discord, Fiverr, MediaFire, and even The Pirate Bay (again, another reason why Tor isn’t good for torrenting). All in all, pretty popular platforms.
What’s more, you can’t use Tor to unblock platforms like Netflix, Hulu, or DirecTV. Slow speeds and IP leaks aside, those websites (and many more) show up on the list of services that block the Tor network.
How to Make Tor Safe
Is Tor safe to use?
Clearly no.
So what can you do to make it more secure?
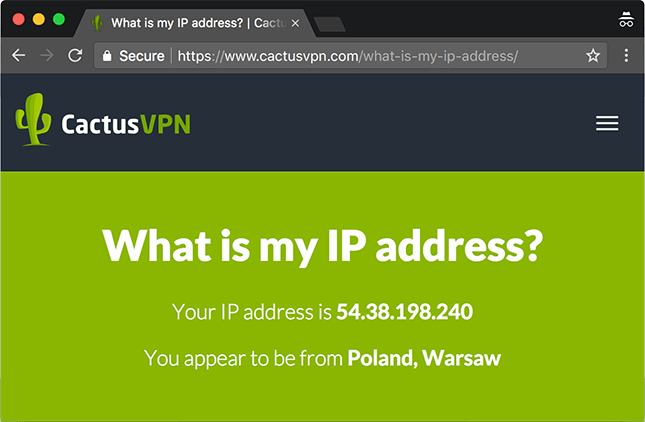
It’s pretty simple – use a VPN. It’s an online service that hides your IP address and encrypts your Internet traffic.
The main advantage is that you get to hide your IP address before connecting to the Tor network. So, even if Tor suffers any IP leaks, data breaches, or has potential backdoors, nobody will be able to see your real address – just the VPN server’s address.
What’s more, even if you come across a malicious node, you won’t need to worry about any hackers seeing your traffic since the VPN already encrypted it. Just make sure you use antivirus/antimalware software too – VPNs can’t protect you from malware and viruses.
Plus, if your government or ISP blocks Tor, a VPN can help you access it. It hides your IP address and your traffic, so nobody can see you accessing the entry node.
Oh, and a VPN makes torrenting safe and reliable, and even lets you bypass geo-restrictions and firewalls with ease.
Alternatively, you could just use the VPN service on its own. You’ll still get to protect your privacy very well, and you won’t need to deal with Tor’s slow speeds.
Need a Powerful VPN?
We’ve got you covered – CactusVPN offers military-grade encryption, secure protocols (SoftEther, OpenVPN, IKEv2, SSTP, L2TP/IPSec), and high-speed servers with unlimited bandwidth.
Plus, we support Tor traffic, and also allow torrenting on nine of our servers.
On top of that, we offer Kill Switch features, DNS leak protection, and access to a Smart DNS service if you want to unblock even more content.
So go ahead – all you need to do is pick a subscription plan and download our user-friendly apps.
Special Deal! Get CactusVPN for $3.5/mo!
And once you do become a CactusVPN customer, we’ll still have your back with a 30-day money-back guarantee.
Is Tor Safe? The Bottom Line
So is Tor safe for your online privacy?
Not really.
The long version of the answer is more complex, but here are the highlights:
- Tor receives funding from the US government.
- Tor devs cooperate with the US government.
- The Tor network suffers IP leaks, and has serious weaknesses.
- The network has a problem with malicious nodes run by hackers and surveillance agencies.
- There are services and methods that single out Tor traffic, making you stand out (which is the opposite of what you want).
- The government doesn’t need any warrants to spy on Tor traffic.
- Tor exit nodes don’t really encrypt your traffic.
Other than that, there are also other issues like Tor speeds being low, Tor not being suitable for torrenting, the network not being able to access websites that use Cloudflare security software, and governments and ISPs being able to outright block access to the network.
If you want to really be safe when using Tor, use a VPN before you connect to the network. That way, you get to enjoy top-notch encryption, and you properly hide your IP address too.



