What Is Obfsproxy?
What Is Obfsproxy?
Obfsproxy is a Tor subproject which can be used to hide the way online traffic looks like.
The main reason why Obfsproxy was developed is because there are countries that use DPI (Deep Packet Inspection) to block VPN connections, or governments that just force ISPs to filter SSL traffic. So, using Obfsproxy can potentially help you avoid getting your traffic filtered and banned.
While initially only built for Tor, Obfsproxy has a feature that allows developers to design, deploy, and test more obfuscating layers that don’t have anything to do with Tor. Because of that, Obfsproxy has started being used to obfuscate OpenVPN traffic too.
How Does Obfsproxy Work?
Simply put, Obfsproxy helps change the way the flow of online traffic looks. Governments or ISPs that use DPI algorithms can classify Internet traffic by protocols by looking at the flow and deciding what it is (HTTP, HTTPS, SSL, VPN, and so on).
The way Obfsproxy works is by having the “obfs2” module add an encryption wrapper around the traffic in question (Tor or OpenVPN). To make sure the encryption is successful, the module uses a handshake process with no recognizable byte patterns.
For example, Obfsproxy would allow you to obfuscate OpenVPN traffic to make it look like regular, harmless HTTP traffic.
Is Obfsproxy 100% Guaranteed to Work?
Not exactly. While it is efficient, it won’t always work perfectly. Keep in mind that even though the traffic flow will be masked, it will still have some recognizable patterns, such as:
- Timing
- Volume
- Packet size
With that information, a thorough entropy test could show government censors or your ISP that the encryption handshake is too random compared to other types of handshakes. In that situation, they could go as far as making it so that only protocols which DPI recognizes are allowed through.
How to Use Obfsproxy for OpenVPN Traffic
The whole OpenVPN Obfsproxy setup process is pretty complex and fairly difficult. Ideally, you should use a VPN service instead of your own VPN server since it’s much easier to obfuscate OpenVPN traffic that way.
WIth that out of the way, here’s a relatively quick overview of how the process usually works on Windows platforms:
Preliminary Steps
First, here’s a list of the things you’ll need before you get started:
- A working OpenVPN server (either one you own or rent, or one offered by a VPN provider).
- The OpenVPN client-side application.
- Python 2.7 (newer versions are okay too, but this one is recommended for Obfsproxy).
- PuTTy, software used for remote access to the OpenVPN server. It’s not necessary if you use a server from a VPN provider.
- Microsoft C++ Compiler for Python 2.7.
- OpenSSL Light.
- The ProxySwitchy Sharp extension (or another good proxy add-on).
Let’s Start With the Client
For starters, install Python 2.7 in the default directory. Afterwards, install the Microsoft C++ Compiler for Python 2.7. If you do some research, you’ll see there are no compilers for newer Python versions, which is why we recommend using Python 2.7.
When you’re done, proceed to install OpenSSL Light (just use the default settings), and then restart your computer.
Now it’s time to handle the OpenVPN files. If you already use a VPN service, the provider will give you access to the config files you need. Otherwise, proceed to installing the OpenVPN client. Afterwards, you’ll find all the files you need in the default directory: “C:/Program Files/OpenVPN/config.” Find the config file you will be using to connect to the OpenVPN server, and open it with Notepad (we recommend running it in Administrator mode). Save the file under a different name so that you’ll have a copy in which you can work without making any mistakes.
Moving on, you’ll be modifying the config file to look like this:
proto tcp-client
remote
port 1194
dev tun1
secret ovpn.key
redirect-gateway def1
ifconfig 10.4.0.2 10.4.0.1
socks-proxy-retry
socks-proxy 127.0.0.1 10194
“your-server-IP” should be replaced with the IP address of your server or the VPN server you’ll be using. On the same line, you can also change the port number to something other than “8080.”
Now, save the file. Make sure it’s saved as a .ovpn file instead of a .txt file. Also, don’t overwrite the original file.
Configuring Obfsproxy
Open the Command Prompt in Administrator mode, and type in the following commands one line at time:
cd C:\Python27\Scripts
pip install –-upgrade pip
pip install obfsproxy
obfsproxy --log-min-severity=info obfs2 --shared-secret=<some-random-key> socks 127.0.0.1:10194
Replace “some-random-key” with the password you want to use.
Make sure you hit Enter after every command. If you get any errors after the second command, you can ignore them.
When you’re finished, the Command Prompt should tell you that it’s listening for Obfsproxy traffic. Every time you’ll want to run Obfsproxy to obfuscate OpenVPN traffic, you’ll need to run the first and last commands, and leave the Command Prompt open.
Optional Proxy Setup
You don’t really need to do this step, but it’s necessary if you plan on using an OpenVPN Obfsproxy connection to watch geo-blocked content on platforms like Netflix. Usually, if you don’t set up the proxy when using Obfsproxy, streaming platforms might be set to the wrong region.
The easiest way to set up the proxy is to do it with the browser extension we linked above. Once it’s installed, just open the ProxySwitchy settings, and create a new profile. Choose “Manual Configuration,” and then enter the following details:
- SOCKS Host – 127.0.0.1
- Port – 8080 (or the port you used in the OpenVPN config file)
- SOCKS v5
Name the profile whatever you want, but don’t turn on the connection yet. Only do that when you’ve established a connection to the OpenVPN server.
Setting Up the Server
Before we start, it’s worth noting that if you run your own OpenVPN server on AWS (Amazon Web Services), you might need to add a new rule that prevents the EC2 instance’s firewall from blocking Obfsproxy traffic.
Moving on, to configure the server, you’ll need to start with PuTTy since you’ll be using it to connect to the server through SSH. You’ll need to check the OpenVPN config file on your filder to make sure port 1194 is open. Python should normally already be installed (especially if you use modern Linux distributions). If it isn’t, proceed to do that.
Afterwards, type in the following commands one line a time in the PuTTy terminal:
sudo yum install gcc
sudo pip install obfsproxy
obfsproxy --log-min-severity=info obfs2 --dest=127.0.0.1:1194 --shared-secret=<some-random-key> server 0.0.0.0:8080
– Older Linux versions might use “apt-get” instead of “yum”. – “some-random-key” must be replaced with the password you use for the client
If everything goes right, the terminal will display a message telling you that the OpenVPN server is listening on a specific port for Obfsproxy traffic.
In case you already have a VPN subscription from a provider whose servers support Obfsproxy, you won’t really need to do anything since the provider would have already taken care of everything on your behalf.
Establishing a Connection Through Obfsproxy
All you need to do is run the OpenVPN GUI/client while Obfsproxy is running on your Command Prompt and your PuTTy terminal. When you see the OpenVPN icon turn green, it means the connection has been established.
Now, if you want to watch some geo-blocked shows, just open your browser (Chrome in this case), and select the profile you created for your ProxySwitchy extension.
Is There a Simpler Way to Do This?
Yes, like we already mentioned, if you use a VPN service, it’s much easier to obfuscate OpenVPN traffic since the server configuration is handled by the provider, and they also offer you access to pre-configured OpenVPN config files.
At most, you’ll just need to install the OpenVPN GUI and configure the Obfsproxy like we mentioned in this article. You can also add the optional proxy in the browser to make sure geo-blocking won’t be a problem.
Need a Powerful Obfuscated VPN?
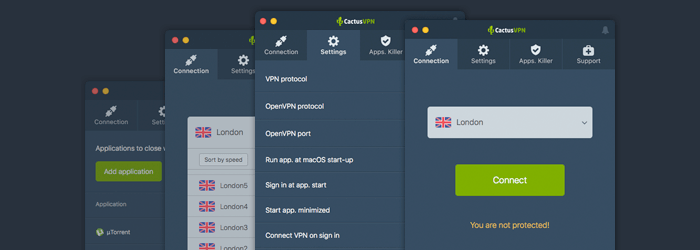
We’ve got just what you need – complete obfsproxy support to help you avoid VPN blocks and throttling.What’s more, CactusVPN is a high-end service that offers access to OpenVPN over TCP and UDP. We offer access to plenty of security features that can help you protect your online data from DPI:
- Military-grade encryption (AES)
- A no-log policy
- DNS leak protection
- A Killswitch and an Apps.Killer
Also, our service has support for Tor traffic as well, so you can use it alongside Tor if you want.
Take Advantage of Secured Connections on Multiple Devices
We designed multiple cross-platform compatible VPN apps that work on the most popular platforms: Windows, macOS, iOS, Android, Android TV, Amazon Fire TV.
Special Deal! Get CactusVPN for $3.5/mo!
And once you do become a CactusVPN customer, we’ll still have your back with a 30-day money-back guarantee.
Conclusion – What Is Obfsproxy?
Obfsproxy is a way to mask Tor and OpenVPN traffic flow to make it look like something else (regular HTTP traffic, for example). Obfsproxy is ideal for people who live in countries where the government is forcing ISPs to use DPI and filter SSL traffic.
Obfuscating OpenVPN traffic is pretty complicated, but it becomes easier if you’re using a third-party VPN service with Obfsproxy support since the provider handles the server and client-side configurations on your behalf. All you’ll need to do is set up the Obfsproxy connection, which is pretty simple to do on Windows and Linux since it only takes a few command lines.
 VPN Obfuscation (Full Guide for Beginners)
VPN Obfuscation (Full Guide for Beginners)
 DNS over HTTPS (Your Handy Guide)
DNS over HTTPS (Your Handy Guide)
