What Is a VPN Protocol & What Is the Best VPN Protocol?

Well, if you’re interested in learning about VPN protocols, this is the right article for you. We’ll discuss what VPN protocols are, go over the general VPN protocol types, and give you a quick overview of what protocols you should use for various online activities.
Table of contents
- What Is a VPN Protocol?
- What VPN Protocol Types Are There?
- VPN Protocol Comparison
- A Quick Overview of the VPN Protocols on Offer
- What Is the Best VPN Protocol?
- What Is the Best VPN Protocol for Torrenting?
- What Is the Fastest VPN Protocol?
- What Is the Most Secure VPN Protocol?
- What Is the Most Stable VPN Protocol?
- What Is the Most Cross-Platform Compatible VPN Protocol?
- What Is the Easiest VPN Protocol to Set Up?
- What Is the Least Resource-Intensive VPN Protocol?
- “So, Which VPN Protocol Should I Use?”
- Need a Service With a Nice Selection of VPN Protocols?
- Conclusion
What Is a VPN Protocol?
VPN protocols represent the processes and sets of instructions VPN providers rely on in order to ensure VPN users get to enjoy stable, secure VPN client-VPN server communications. At its core, a VPN protocol is basically a mix of transmission protocols and encryption standards.
What VPN Protocol Types Are There?
At the moment of writing of this article, you’re most likely to see VPN providers offering access to the following VPN protocols:
- PPTP
- L2TP/IPSec
- IKEv2/IPSec
- IPSec
- SSTP
- OpenVPN
- SoftEther
- WireGuard®
VPN Protocol Comparison
| VPN Protocol | Connection Speed | Level of Encryption | Connection Stability | Media Streaming | Torrent Downloading | Compatible With | Available in CactusVPN App |
| OpenVPN TCP | Medium | Very Good | Stable | Medium | Good | Most OSs and devices | On Windows, Android, and Fire TV |
|---|---|---|---|---|---|---|---|
| OpenVPN UDP | Fast | Very Good | Medium | Good | Good | Most OSs and devices | On Windows, Android, and Fire TV |
| Wireguard | Fast | Very Good | Very Stable | Good | Good | Windows, macOS, iOS, Android and Linux | On Windows, macOS, Android, Fire TV, and iOS |
| IKEv2/IPSec | Very Fast | Good | Very Stable | Good | Good | Most OSs and devices | On Windows, macOS, and iOS |
| IPSec | Medium | Good | Stable | Good | Good | Most OSs and devices | No |
| SSTP | Fast | Good | Very Stable | Medium | Good | Windows, Ubuntu, Android, and routers | On Windows |
| SoftEther | Very Fast | Very Good | Very Stable | Good | Good | Most OSs and devices | No |
| L2TP/IPSec | Medium | Medium | Stable | Good | Medium | Most OSs and devices | On Windows |
| PPTP | Very Fast | Poor | Very Stable | Good | Poor | Most OSs and devices | On Windows |
A Quick Overview of the VPN Protocols on Offer
If you want to learn a bit more about every VPN protocol we outlined above, this section is just what you need. Here is what you should know – in short – about all the protocols VPN providers use:
1. PPTP
PPTP stands for Point-to-Point Tunneling Protocol, and it’s a VPN protocol that was developed by Microsoft back in the ‘90s. Nowadays, it’s pretty popular for people who want to stream geo-restricted content because of its high speeds. Besides that, the VPN is also easy to configure and is already built into most platforms.
Pretty much all VPN providers offer access to PPTP, though you should avoid providers who only offer PPTP. Why? Because it barely offers any reliable security. In fact, it’s pretty safe to assume that PPTP was cracked by the NSA. What’s more, PPTP can also be blocked by firewalls with little effort most of the time.
In case you’d like to read more about the PPTP encryption protocol, feel free to check out this article.
2. L2TP/IPSec
Generally considered an improvement over PPTP, L2TP/IPSec is basically an extension of the PPTP protocol, with the main difference being that it uses double encapsulation:
- The first encapsulation sets up the PPP connection.
- The second encapsulation has the actual IPSec encryption.
While double encapsulation can make L2TP/IPSec more secure, it can also make it slower than PPTP since traffic needs to first be converted into L2TP form, and afterwards you also have an extra layer of encryption added on top.
Overall, the protocol is pretty secure (especially if it uses the AES cipher), though it is worth mentioning that L2TP on its own provides no encryption, which is why it’s always paired up with IPSec.
Like PPTP, L2TP/IPSec is normally easy to configure, and it’s already built into many existing platforms. So, you’ll see many VPN providers offering access to it. However, most providers will normally have to further configure the protocol to make sure it can’t be blocked by NAT firewalls (since it can only use UDP port 500 for establishing a connection).
On the plus side, that kind of setup ensures L2TP/IPSec can’t be exploited by man-in-the-middle attacks.
While there have been claims that the NSA has cracked or weakened this VPN encryption protocol, there is no proof to back them up. Still, it’s worth noting that said claims come from Edward Snowden himself.
To learn more about L2TP/IPSec, read this article.
3. IPSec
IPSec is a secure network protocol suite that’s used to encrypt data packets which are sent over an IP network (a communication network comprised of one or more devices which use the Internet Protocol to send and receive data).
IPSec is pretty popular due to its high security (courtesy of its Authentication Header and Encapsulating Security Payload mechanisms) and the fact that it can encrypt traffic without the end point application being aware of it.
Regarding downsides, IPSec can be difficult to configure, so errors can arise if the VPN provider doesn’t have enough experience with it. In VPN technology, IPSec is often used alongside L2TP and IKEv2. Also, like we mentioned above, there have been claims – though, unfounded – that the NSA has intentionally weakened the protocol.
If you want to read more about IPSec, follow this link.
4. IKEv2
Developed by both Microsoft and Cisco and based on IPSec, IKEv2 is relatively fast, stable, and safe (if a cipher like AES is used). Plus, it even works natively on Blackberry devices. And since it has support for MOBIKE, it handles network changes very well. What does that mean? Well, that – for example – when you switch from a WiFi connection to a data plan connection on your mobile, the VPN connection will remain stable throughout the process.
Funnily enough, IKEv2 is not technically a VPN protocol, but it does behave like one, and it helps control the IPSec key exchange.
Regarding downsides, IKEv2 can be hard to implement on the VPN server side, so an inexperienced or unprepared VPN provider could make mistakes which can result in connectivity or security problems. Also, some users don’t like that Microsoft was involved in its creation. That, and IKEv2 can potentially be blocked by some firewalls.
Interested in finding out more about IKEv2? Then be sure to check out our article on it.
5. OpenVPN
An open-source protocol, OpenVPN is one of the most popular VPN protocols among users. It’s very secure, configurable, and works on multiple platforms. Furthermore, OpenVPN is very difficult to block because OpenVPN traffic is extremely difficult to tell apart from HTTPS/SSL traffic.
Oh, and the OpenVPN protocol can also run on any port (including the 443 HTTPS port) and use both UDP and TCP protocols.
The protocol’s main downside seems to be the fact that using it with strong encryption ciphers can sometimes slow down connection speeds. Still, that problem can sometimes be solved by having OpenVPN use the UDP protocol since it’s faster.
Besides that, OpenVPN requires third-party software since it isn’t natively integrated into operating systems or various platforms, and setting it up can be difficult. Luckily, that’s not a big problem for the average user since VPN clients serve as the needed third-party software.
In case you’re looking to read more about OpenVPN, check out this link.
6. SoftEther
Compared to most VPN encryption protocols (except Wireguard), SoftEther is relatively new. The protocol started out as a simple project at the University of Tsukuba, but ended up growing into a large open-source multi-protocol VPN software project.
“Wait, what do you mean multi-protocol VPN software?”
Well, at this point, it’s important to make one clear distinction – SoftEther can either refer to the VPN protocol or the VPN server:
- The SoftEther VPN server can support a large number of VPN protocols, like SSTP, OpenVPN, L2TP/IPSec, IPSec, and the SoftEther VPN protocol (hence the “multi-protocol” bit)
- The SoftEther VPN protocol uses SSL 3.0 for secure VPN client-server communications. The protocol contains various technical improvements that make it faster and more secure.
Despite it being new, SoftEther has quickly become popular with VPN users due to the fact that it’s very secure (SoftEther uses AES-256), stable, and surprisingly fast. What’s more, it’s also free to use, and it works across multiple operating systems (including FreeBSD and Solaris) – not to mention it’s one of the few VPN protocols to have working clients on Linux.
Furthermore, SoftEther even has functions that OpenVPN doesn’t, such as Dynamic DNS Function, RPC Over HTTPS Management, and GUI Management (just to name a few examples).
Right now, the only drawbacks that might be worth mentioning are the fact that SoftEther has no native OS support, and that – for some reason – there are VPN providers who don’t offer it as an option. Also, since it’s a software-based solution, a VPN provider can’t really offer you direct access to the protocol. Instead, you will need to install SoftEther on your device, and connect to the provider’s servers.
If you’d like to read more about SoftEther, we’ve already written an in-depth article on it.
7. SSTP
SSTP stands for Secure Socket Tunneling Protocol, and it was introduced by Microsoft with Windows Vista. Despite that, it still works on other operating systems too (like Linux and Android). SSTP is significantly superior than PPTP when it comes to security since it can be configured with AES encryption.

Also, the SSTP VPN protocol is often compared to OpenVPN in terms of benefits since it uses SSL 3.0, thus allowing it to bypass censorship by using port 443 (the HTTPS traffic port).
Despite that, SSTP isn’t as popular as OpenVPN because it’s owned by Microsoft, tends to mostly work well only on Windows platforms, and is not open-source.
Want to read more about SSTP? Then check out our article on it.
8. Wireguard
WireGuard is the newest addition (it was made public in 2018). Despite being such a new protocol, it became popular fast. It underwent development and testing, aced numerous security audits, and is now ready for deployment.
The protocol boasts state-of-the-art security since it only uses modern cryptographic algorithms. It’s also very transparent since it’s open-source, so anyone can inspect its code. What’s more, WireGuard offers lighting-fast speeds thanks to its lightweight code base and ability to efficiently use all CPU cores.
For more information about Wireguard, check out this article.
Need a Service With a Nice Selection of VPN Protocols?
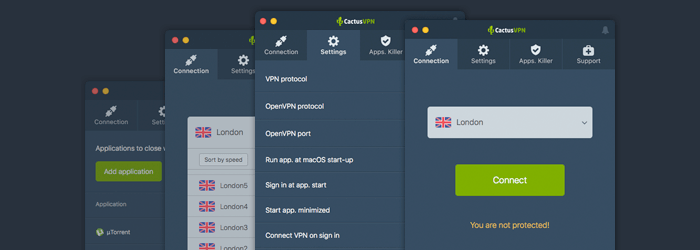
We’ve got you covered – CactusVPN provides access to the most popular VPN protocols there are: OpenVPN, Wireguard, SoftEther, IKEv2, SSTP, L2TP/IPSec and PPTP.
Choosing which VPN protocol you want to use is extremely simple – just use the drop-down menu in our VPN app to make your choice before connecting to one of our servers, and you’re good to go. No complex setup processes at all.
Enjoy Top-Notch Online Security Too
Our VPN protocols use AES-256 encryption ciphers to make sure your personal data and Internet traffic are safe and sound.
Plus, we provide access to a reliable Kill Switch as well, so that you can enjoy peace of mind while browsing the web knowing that your traffic will not be exposed even if you happen to encounter connectivity issues.
Oh, and on top of that all we also enforce a strict no-logging policy at our company, meaning you don’t need to worry about anyone here at CactusVPN seeing what you do online.
Special Deal! Get CactusVPN for $3.5/mo!
And once you do become a CactusVPN customer, we’ll still have your back with a 30-day money-back guarantee.
What Is the Best VPN Protocol?
This is a pretty difficult question to answer – mostly because what counts as the “best VPN protocol” solely depends on what you want to do on the Internet. What might be considered the best VPN protocol by some people, might be seen as a sub-par encryption protocol by others, after all.
So, to offer you a decent answer, we’ll be looking at which VPN protocols work best for certain online activities or situations:
What Is the Best VPN Protocol for Torrenting?
When it comes to torrenting with a VPN, you are definitely going to need a VPN protocol that is stable, fast, and secure. Based on that, you should use IKEv2 or WireGuard. SoftEther is also a speedy option, but it’s not for all users since it requires an initial setup that might seem difficult to some.
L2TP/IPSec is also a good option since it’s pretty secure and fast. But don’t use PPTP! While it’s very fast, its encryption is too weak (the NSA can actually crack it).
You could also try using OpenVPN UDP to download torrents, though we recommend only doing that if you use a VPN that offers a Kill Switch since it doesn’t offer perfect stability. And you definitely don’t want your torrenting activities being exposed if your VPN connection suddenly goes down.
Our Recommendation: WireGuard, IKEv2, OpenVPN UDP, or SoftEther (for advanced users)
DISCLAIMER: We here at CactusVPN don’t encourage illegal copyright infringement and illegal torrenting. However, we do understand that – for some people – file-sharing is the only possible way to get access to entertainment (movies, TV shows, video games) and work or school files.
What Is the Fastest VPN Protocol?
For a long time, PPTP was considered the go-to option if you were looking for a fast VPN protocol. Nowadays, it still is a very fast VPN protocol that’s often used for streaming geo-blocked content. However, that speed comes with the price of a severe lack of encryption, leaving you virtually exposed online.

Here are some much better alternatives to PPTP – IKEv2 and WireGuard. They both offer very fast speeds and powerful security to boot. L2TP/IPSec is speedy too, but usually slower than IKEv2 and WireGuard.
SoftEther is also a good option. Apparently, this VPN protocol is four times faster than the PPTP protocol, and thirteen times faster than the OpenVPN protocol. Allegedly, that’s because SoftEther was written with high-speed throughput in mind. It’s also very secure and available on multiple platforms, but there aren’t many providers that support it. What’s more, you can’t use it inside a VPN app. Instead, you need to download, install, and configure the SoftEther client.
Of course, you could always use PPTP too if you want, but keep in mind you must make sure none of your sensitive data would be endangered if you were to do that. So don’t use it to log into your email, bank, or Netflix account, for example. Only use it to stream content.
Our Recommendation: WireGuard, IKEv2, and SoftEther (not for inexperienced users, though)
What Is the Most Secure VPN Protocol?
OpenVPN would be our first choice. It offers 256-bit encryption, it doesn’t require IP stack and kernel operation since it runs in userspace (providing better memory protection), and it also runs a custom security protocol that’s based on TLS and SSL.
You’re better off using a VPN provider that also offers a Kill Switch (that goes for any VPN protocol), but OpenVPN TCP is pretty stable so there shouldn’t be any problems.
SoftEther is a decent option as well. The security you get to enjoy is pretty much on par with the protection you get with OpenVPN. Using SoftEther for top-notch Internet security comes down to whether or not you’re okay with using a newer VPN protocol instead of the legacy OpenVPN one.
The same goes for WireGuard. It’s the newest VPN protocol, but multiple audits already showed how secure it is. Plus, it uses modern algorithms (like ChaCha20, BLAKE2s, and Curve 25519), and replaces cryptographic agility (the ability to choose between encryption) with crypto versioning (fixed encryption). That way, it eliminates potential misconfigurations which can weaken the encryption.
IKEv2 is also a good choice if you use BlackBerry devices, and it encrypts the data twice. L2TP/IPSec does that as well and is generally considered safe, but we wouldn’t really recommend it over the rest of the VPN protocols we mentioned for this particular context.
As for Wireguard, it’s true it’s a secure protocol, but it’s still in the experimental phase so it’s hard to rely on it for online security for now.
Besides that, SSTP works well too. It just depends on whether or not you’re bothered by the fact that it’s not open-source, and that it’s solely controlled by Microsoft – a company that has given the NSA access to encrypted messages before.
Our Recommendation: OpenVPN, WireGuard, IKEv2 (on smartphones) or SoftEther
What Is the Most Stable VPN Protocol?
IKEv2 is an excellent choice when it comes to stability on mobile devices since it can actually resist network changes. Network admins can block it easily, though, since it only uses a few UDP ports.
WireGuard performs very well too, but it only uses UDP ports, so it can be blocked. On the plus side, it uses a ton of ports, so it’s unlikely that a network admin would block all of them.
OpenVPN (over TCP), SoftEther, and SSTP handle stability excellently since they can use port 443 (the HTTPS port).
What’s more, SoftEther does very well too given that it was made based on the idea that it will run 24/7 permanently once it’s started up. Its code was written in such a way as to prevent both memory leaks and various crashes. Even if something goes wrong, SoftEther is programmed to re-start automatically as fast as possible.
Other stable VPN protocols include OpenVPN (when it uses the TCP port), SSTP, and L2TP/IPSec. PPTP is also pretty stable, but keep in mind it can be blocked by firewalls with ease sometimes.
PPTP and L2TP/IPSec are pretty stable too, but it’s easy to block them – you just have to block the ports they use or disable VPN Passthrough for those protocols to prevent the VPN app from communicating with the VPN server.
Our Recommendation: IKEv2, SoftEther (requires additional setup, though), or OpenVPN TCP
What Is the Most Cross-Platform Compatible VPN Protocol?
PPTP seems to be the most natively supported VPN protocol – being available across multiple operating systems and devices. However, it’s worth noting that due to its security weakness, PPTP might no longer be supported on newer devices and operating systems. For example, the VPN protocol is no longer natively supported on macOS Sierra (and higher versions).
A good alternative to PPTP is L2TP/IPSec which is natively available on numerous platforms as well. IKEv2 is a good option too – especially since it works on BlackBerry devices.
OpenVPN doesn’t have native support on operating systems and other devices, but it’s easily available through third-party software like VPN clients. WireGuard works on the most popular operating systems too (Windows, macOS, Linux, iOS, Android).
Our Recommendation: L2TP/IPSec, OpenVPN, IKEv2, and WireGuard
What Is the Easiest VPN Protocol to Set Up?
For now, PPTP seems to be the easiest VPN protocol to configure simply because it’s natively built into so many platforms. L2TP/IPSec and IKEv2 are fairly simple to set up as well because of the same reason.
SSTP is also very easy to manage, though only on Windows platforms. WireGuard has a simple setup as well – especially on Linux. Most reviews claim it’s easier to manage than OpenVPN.
SoftEther is not extremely difficult to set up compared to OpenVPN since it comes with an easy-to-use installer and it has GUI Management Tools. But compared to the other VPN protocols mentioned above, there’s still some work involved.
Of course, if you use third-party VPN software, you get easy access to any VPN protocol you want as long as the VPN provider offers it, and as long as it works on your device or operating system – except for SoftEther since you need to install its software on your device, and connect to the VPN provider’s servers manually.
Our Recommendation: PPTP, L2TP/IPSec, WireGuard, or IKEv2
What Is the Least Resource-Intensive VPN Protocol?
Without a doubt, PPTP is one of the least resource-intensive options simply because it offers such inferior encryption which doesn’t eat up a lot of CPU power.
SSTP is normally a better choice, though, because it eats up less resources while also offering decent security – all thanks to the fact that it’s strongly integrated into Windows platforms. If you use a different operating system or device, you could try OpenVPN instead of PPTP since it can optimize its processing power usage.
But we think WireGuard is the perfect choice for any platform because it’s optimized to efficiently use CPU cores. Also, it has a very small code base (only around 4,000 lines), so it’s very lightweight.
Our Recommendation: WireGuard
“So, Which VPN Protocol Should I Use?”
Hard to say – it all really depends on what you want to do on the Internet. Here’s a quick list that showcases what each VPN protocol is best used for that might help you out when having to make such a decision:
- PPTP is best used when you just want fast access to geo-blocked content. Ideally, you shouldn’t use it when you’re logged into other accounts that contain sensitive information (like your bank account, for example).
- L2TP/IPSec is basically an improved version of PPTP, so you can use it when you want to download torrents, access geo-blocked content, and browse the Internet safely, and don’t mind a potential drop in connection speeds.
- IKEv2 is a great option if you use your mobile device (especially if it’s a BlackBerry device) a lot since your VPN connection remains stable when switching from WiFi networks to your data plan. It’s also ideal if you’re looking to secure your online traffic and enjoy decent speeds.
- SSTP is a good option if you’re a Windows user, and you want to enjoy decent online security and speed without the protocol eating up too much of your CPU power.
- OpenVPN should be your go-to option if you want a secure, stable online connection. If you’re interested in better speeds, you can use OpenVPN over UDP.
- SoftEther is an excellent OpenVPN alternative, and it’s the right choice if you don’t mind a newer VPN protocol, and want to enjoy secure, stable, fast connections.
- WireGuard is ideal if you want to protect your data with modern encryption ciphers while also enjoying really fast speeds on most platforms (Windows, macOS, Linux, iOS, Android).
Conclusion
A VPN protocol is a set of rules that are used to negotiate a connection between the VPN client and the VPN server. At the moment, these are the VPN protocols you are most likely to see being used by VPN providers:
- PPTP
- SSTP
- L2TP/IPSec
- IKEv2/IPSec
- OpenVPN
- SoftEther
- Wireguard
Generally, OpenVPN, WireGuard, IKEv2, and SoftEther are the ideal VPN protocols to use if you’re looking to enjoy a secure online experience. SSTP and L2TP/IPSec are good alternatives if you’re not happy with those options.
If you want security and speed, though, stick to IKEv2, WireGuard, and SoftEther. L2TP/IPSec is safe to use too, but it kind of offers the same level of security like IKEv2, but is slower. So there’s no reason not to use IKEv2 if you can.
PPTP should only be used when you need fast connection speeds and are sure your privacy won’t be in danger (since it has poor encryption).
Ideally, you should pick a VPN provider that lets you choose between multiple VPN protocols.
“WireGuard” is a registered trademark of Jason A. Donenfeld.
 What Is PFS (Perfect Forward Secrecy)?
What Is PFS (Perfect Forward Secrecy)?
 What Is PPTP? (Everything You Need to Know)
What Is PPTP? (Everything You Need to Know)
