What Is IKEv2?

The IKEv2 VPN protocol has become more and more popular over the past years - especially with mobile users. It’s not hard to see why given how efficient and secure the protocol is.
But what is IKEv2, actually? And how does it manage to offer online users a safe online experience? Well, here’s everything you need to know about that (and more):
Table of contents
What Is IKEv2?
IKEv2 (Internet Key Exchange version 2) is a VPN encryption protocol that handles request and response actions. It makes sure the traffic is secure by establishing and handling the SA (Security Association) attribute within an authentication suite – usually IPSec since IKEv2 is basically based on it and built into it.
IKEv2 was developed by Microsoft together with Cisco, and it’s the successor to IKEv1.
Here’s How IKEv2 Works
Like any VPN protocol, IKEv2 is responsible for establishing a secure tunnel between the VPN client and the VPN server. It does that by first authenticating both the client and the server, and then agreeing on which encryption methods will be used
We already mentioned that IKEv2 handles the SA attribute, but what is SA? Simply put, it’s the process of establishing security attributes between two network entities (in this case, the VPN client and the VPN server). It does that by generating the same symmetric encryption key for both entities. Said key is then used to encrypt and decrypt all the data that travels through the VPN tunnel.
General Technical Details About IKEv2
- IKEv2 supports IPSec’s latest encryption algorithms, alongside multiple other encryption ciphers.
- Generally, the IKE daemon (a program that runs as a background process) runs in the user space (system memory dedicated to running applications) while the IPSec stack runs in kernel space (the core of the operating system). That helps boost performance.
- The IKE protocol uses UDP packets and UDP port 500. Normally, four to six packets are necessary for creating the SA.
- IKE is based on the following underlying security protocols:
- The IKEv2 VPN protocol supports MOBIKE (IKEv2 Mobility and Multihoming Protocol), a function that allows the protocol to resist network changes.
- IKEv2 supports PFS (Perfect Forward Secrecy).
- While IKEv2 was developed by Microsoft together with Cisco, there are open-source implementations of the protocol (like OpenIKEv2, Openswan, and strongSwan).
- IKE uses X.509 certificates when it handles the authentication process.
IKEv1 vs. IKEv2
Here’s a list of the main differences between IKEv2 and IKEv1:
- IKEv2 offers support for remote access by default thanks to its EAP authentication.
- IKEv2 is programmed to consume less bandwidth than IKEv1.
- The IKEv2 VPN protocol uses encryption keys for both sides, making it more secure than IKEv1.
- IKEv2 has MOBIKE support, meaning it can resist network changes.
- IKEv1 doesn’t have built-in NAT traversal like IKEv2 does.
- Unlike IKEv1, IKEv2 can actually detect if a VPN tunnel is “alive” or not. That feature allows IKEv2 to automatically re-establish a dropped connection.
- IKEv2 encryption supports more algorithms than IKEv1.
- IKEv2 offers better reliability through improved sequence numbers and acknowledgements.
- The IKEv2 protocol will first determine if the requester actually exist before proceeding to perform any actions. Because of that, it’s more resistant to DoS attacks.
Is IKEv2 Secure?
Yes, IKEv2 is a protocol that’s safe to use. It supports 256-bit encryption, and can use ciphers like AES, 3DES, Camellia, and ChaCha20. What’s more, IKEv2/IPSec also supports PFS + the protocol’s MOBIKE feature makes sure your connection won’t be dropped when changing networks.
Another thing worth mentioning is that IKEv2’s certificate-based authentication process makes sure that no action is taken until the identity of the requester is determined and confirmed.
Also, it’s true that Microsoft worked on IKEv2, and that’s not a very trustworthy corporation. However, they didn’t work on the protocol alone, but together with Cisco. Also, IKEv2 isn’t completely closed-source since open-source implementations of the protocol exist.
Still, we should address three security-related issues regarding IKEv2/IPSec:
1. Password Issues
Back in 2018, some research came to light that highlighted the potential security weaknesses of both IKEv1 and IKEv2. The IKEv1 problems shouldn’t really concern you as long as you don’t use the protocol. As for the IKEv2 issue, it seems that it could be relatively easily hacked if the login password that is used by it is weak.
Still, that normally isn’t a huge security concern if you are using a strong password. The same can be said if you are using a third-party VPN service since they’ll be handling the IKEv2 login passwords and authentication on your behalf. As long as you choose a decent, secure provider, there should be no problems.
2. NSA Exploitation of ISAKMP
The German magazine Der Spiegel released leaked NSA presentations that claimed the NSA was able to exploit IKE and ISAKMP to decrypt IPSec traffic. In case you didn’t know, ISAKMP is used by IPSec to implement VPN service negotiations.
Unfortunately, the details are a bit vague, and there’s no exact way to guarantee that the presentations are valid. In case you’re very worried about this issue, you should avoid setting up the connection on your own and instead get an IKEv2 connection from a reliable VPN provider who uses powerful encryption ciphers.
3. Man-in-the-Middle Attacks
It seems that IPSec VPN configurations that are intended to allow multiple configurations to be negotiated could potentially be subjected to downgrade attacks (a type of Man-in-the-Middle attacks). That can happen even if IKEv2 is used instead of IKEv1.
Luckily, the problem can be avoided if stricter configurations are used, and if the client systems are carefully segregated on multiple service access points. What that means in English is that if the VPN provider does its job right, you shouldn’t have to worry about this.
Is IKEv2 Fast?
Yes, IKEv2/IPSec offers decent online speeds. In fact, it’s one of the fastest VPN protocols that are available to online users – potentially even as fast as PPTP or SoftEther. And that’s all thanks to its improved architecture and efficient response/request message exchange process. Also, the fact that it runs on UDP port 500 ensures there is low latency.
Better yet, due to its MOBIKE feature, you don’t need to worry about IKEv2’ speeds going down or being interrupted when you change networks.
IKEv2 Advantages and Disadvantages
Advantages
- IKEv2 security is quite strong since it supports multiple high-end ciphers.
- Despite its high security standard, IKEv2 offers fast online speeds.
- IKEv2 can easily resist network changes due to its MOBIKE support, and can automatically restore dropped connections.
- IKEv2 is natively available on BlackBerry devices, and can be configured on other mobile devices too.
- Setting up an IKEv2 VPN connection is relatively simple.
Disadvantages
- Since IKEv2 only uses UDP port 500, a firewall or network admin could block it.
- IKEv2 doesn’t offer as much cross-platform compatibility like other protocols (PPTP, L2TP, OpenVPN, SoftEther).
What Is IKEv2 VPN Support?
IKEv2 VPN support is basically when a third-party VPN provider offers access to IKEv2/IPSec connections through its service. Fortunately, more and more VPN providers have started recognizing how important this protocol is to mobile users, so you’re more likely to find services that offer IKEv2 connections now than before.
Still, we do recommend choosing a VPN provider who offers access to multiple VPN protocols. While IKEv2/IPSec is a great protocol on mobile, it doesn’t hurt to have a decent backup (like OpenVPN or SoftEther) when you’re using other devices at home
Need an IKEv2 VPN You Can Rely on?
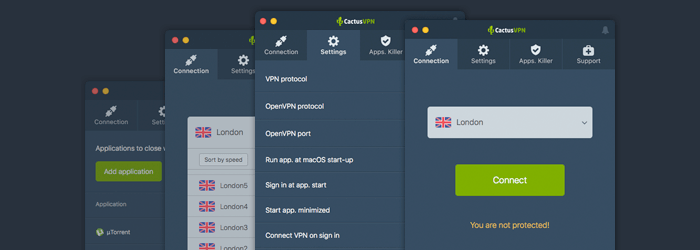
CactusVPN is just the service you need. We offer high-speed IKEv2/IPSec connections that are secured with AES, 256-bit NIST Elliptic Curve, SHA-256, and RSA-2048. What’s more, we protect your privacy by not logging any of your data, and our service comes equipped with DNS leak protection and a Killswitch too
Besides that, you should know that IKEv2 won’t be the only option at your disposal. We also offer access to other VPN protocols: OpenVPN, SoftEther, SSTP, L2TP/IPSec and PPTP.
Set Up an IKEv2 Connection With Extreme Ease
You can set up an IKEv2/IPSec tunnel with just a few clicks if you use CactusVPN. We offer multiple cross-platform compatible clients which are very user-friendly.
Special Deal! Get CactusVPN for $3.5/mo!
And once you do become a CactusVPN customer, we’ll still have your back with a 30-day money-back guarantee.
IKEv2 vs. Other VPN Protocols
Before we start, we should mention that when we’ll be discussing IKEv2 in this section, we’ll be referring to IKEv2/IPSec since that’s the protocol VPN providers generally offer. Also, IKEv2 can’t normally be used on its own since it’s a protocol built within IPSec (which is why it’s paired up with it). With that out of the way, let’s begin:
1. IKEv2 vs. L2TP/IPSec
Both L2TP and IKEv2 are generally paired up with IPSec when they’re offered by VPN providers. That means they tend to offer the same level of security. Still, while L2TP/IPSec is closed-source, there are open-source implementations of IKEv2. That, and Snowden has claimed that the NSA have weakened L2TP/IPSec, though there’s no real evidence to back that claim up.
IKEv2/IPSec is faster than L2TP/IPSec since L2TP/IPSec is more resource-intensive due to it double encapsulation feature, and also takes longer to negotiate a VPN tunnel. And while both protocols pretty much use the same ports due to being paired up with IPSec, L2TP/IPSec might be easier to block with a NAT firewall since L2TP tends to sometimes not work well with NAT – especially if L2TP Passthrough isn’t enabled on the router.
Also, while we’re on the topic of stability, it should be mentioned that IKEv2 is far more stable than L2TP/IPSec since it can resist network changes. Basically, that means you can switch from a WiFi connection to a data plan connection without the IKEv2 connection going down. Not to mention that even if an IKEv2 connection goes down, it’s restored immediately.
As for accessibility, L2TP/IPSec is natively available on more platforms than IKEv2/IPSec is, but IKEv2 is available on BlackBerry devices.
Overall, it would seem that IKEv2/IPSec is a better choice for mobile users, whereas L2TP/IPSec works well for other devices.
In case you’d like to find out more about L2TP, follow this link.
2. IKEv2 vs. IPSec
IKEv2/IPSec is pretty much better in all regards than IPSec since it offers the security benefits of IPSec alongside the high speeds and stability of IKEv2. Also, you can’t really compare IKEv2 on its own with IPSec since IKEv2 is a protocol that’s used within the IPSec protocol suite. Also, IKEv2 is essentially based on IPSec tunneling.
If you’d like to read more about IPSec, check out our article about it.
3. IKEv2 vs. OpenVPN
OpenVPN is extremely popular with online users due to its enhanced security, but you should know that IKEv2 can offer a similar level of protection. It’s true that IKEv2 secures information at the IP level while OpenVPN does that at the Transport level, but it’s not really something that should make a huge difference.
However, we can’t deny the fact that OpenVPN being open-source makes it a more appealing option than IKEv2. Of course, that no longer becomes such a huge problem if you use open-source implementations of IKEv2.
In terms of online speeds, IKEv2 is usually faster than OpenVPN – even when OpenVPN uses the UDP transmission protocol. On the other hand, it’s much harder for a network admin to block OpenVPN connections since the protocol uses port 443, which is the HTTPS traffic port. IKEv2, unfortunately, uses only UDP port 500 which a network admin can block without having to worry about stopping other vital online traffic.
As for connection stability, both protocols fare pretty well, but IKEv2 surpasses OpenVPN on mobile devices since it can resist network changes. It’s true that OpenVPN can be configured to do the same with the “float” command, but it’s not as efficient and stable as IKEv2 is.
Regarding cross-platform support, IKEv2 is a bit behind OpenVPN, but it does work on BlackBerry devices. Also, IKEv2 is usually a bit easier to set up since it’s normally natively integrated into the platforms it’s available on.
Want to find out more about OpenVPN? Here’s an in-depth guide we wrote about it
4. IKEv2 vs. PPTP
IKEv2 is generally a much better choice than PPTP simply because it’s way more secure than it. For one, it offers support for 256-bit encryption keys and high-end ciphers like AES. Also, as far as we know, IKEv2 traffic has yet to be cracked by the NSA. The same can’t be said about PPTP traffic.
Besides that, PPTP is much less stable than IKEv2. It can’t resist network changes with ease like IKEv2, and – even worse – it’s extremely easy to block with a firewall – especially a NAT firewall since PPTP isn’t natively supported on NAT. In fact, if PPTP Passthrough isn’t enabled on a router, a PPTP connection can’t even be established.
Normally, one of PPTP’s main highlights that make it stand out from its competition is its very high speed. Well, the funny thing is that IKEv2 is actually capable of offering speeds similar to the ones offered by PPTP.
Basically, the only way PPTP is better than IKEv2 is when it comes to availability and ease of setup. You see, PPTP is natively built into tons of platforms, so configuring a connection is extremely simple. Still, that might not be the case in the future since native support for PPTP has started being removed from newer versions of some operating systems. For example, PPTP is no longer natively available on iOS 10 and macOS Sierra.
All in all, you should always pick IKEv2 over PPTP if possible.
If you’d like to learn more about PPTP, and find out why it’s such a risky option, follow this link.
5. IKEv2 vs. WireGuard®
Your data should be safe with both protocols. But if you want a more modern approach to cryptography, you should stick to WireGuard. And while IKEv2 has some open-source implementations, most providers don’t use them.
Like L2TP/IPSec, IKEv2/IPSec is easier to block because it uses fewer ports: UDP 500, ESP IP Protocol 50, UDP 4500. On the plus side, IKEv2 offers MOBIKE – a feature that lets the protocol resist network changes. So if you switch from WiFi to mobile data on mobile, your VPN shouldn’t disconnect.
Both protocols are very fast. We sometimes have faster speeds with WireGuard, but not by much.
They both work on most operating systems. The only difference is that IKEv2/IPSec is natively available on BlackBerry devices.
Whether you need speed or security (or both), either protocol is an excellent choice. Maybe stick to IKEv2/IPSec if you’re using a smartphone since the MOBIKE feature is really useful.
In case you’d like to learn more about Wireguard, here’s a link to our guide.
6. IKEv2 vs. SoftEther
Both IKEv2 and SoftEther are fairly secure protocols, and even though SoftEther might be more trustworthy because it’s open source, you can find open-source implementations of IKEv2 too. Both protocols are also very fast, though SoftEther might be a bit speedier than IKEv2.
When it comes to stability, things are different. For one, SoftEther is much harder to block with a firewall because it runs on port 443 (the HTTPS port). On the other hand, IKEv2’s MOBIKE feature allows it to seamlessly resist network changes (like when you switch from a WiFi connection to a data plan one).
It might also interest you to know that while the SoftEther VPN server has support for the IPSec and L2TP/IPSec protocols (among others), it doesn’t have any support for the IKEv2/IPSec protocol.
In the end, SoftEther is pretty much a better option than IKEv2, though you might prefer using IKEv2 if you’re a mobile user – especially since it’s available on BlackBerry devices.
If you’d like to find out more about SoftEther, check out this link.
7. IKEv2 vs. SSTP
IKEv2 and SSTP offer a similar level of security, but SSTP is much more firewall-resistant since it uses TCP port 443, a port that can’t be normally blocked. On the other hand, SSTP isn’t available on as many platforms as IKEv2 is. SSTP is only built into Windows systems (Vista and higher), and it can further be configured on routers, Linux, and Android. IKEv2 works on all those platforms and more (macOS, iOS, FreeBSD, and BlackBerry devices).
Both IKEv2 and SSTP were developed by Microsoft, but IKEv2 was developed by Microsoft together with Cisco. That makes it a bit more trustworthy than SSTP which is solely owned by Microsoft – a company that has handed the NSA access to encrypted messages in the past, and that is also part of the PRISM surveillance program.
In terms of connection speeds, both protocols are pretty tied, but it’s very likely that IKEv2 is faster than SSTP. Why? Because SSTP’s speeds are often compared to OpenVPN’s speeds, and we’ve already mentioned that IKEv2 is faster than OpenVPN. Besides that, there’s also the fact that SSTP only uses TCP, which is slower than UDP (the transmission protocol used by IKEv2).
Interested in learning more about SSTP? Here’s an article we wrote about it.
So, Is the IKEv2 Protocol a Good Choice?
Yes, IKEv2 is a good option for a safe, smooth online experience. We’d still recommend you use either OpenVPN or SoftEther, but if those options aren’t available for some reason, IKEv2 works well too – especially if you use your mobile and you travel quite often.
What Is IKEv2? In Conclusion
IKEv2 is both a VPN protocol and an encryption protocol used within the IPSec suite.
Essentially, it’s used to established and authenticate a secured communication between a VPN client and a VPN server.
IKEv2 is very safe to use, as it has support for powerful encryption ciphers, and it also improved all the security flaws that were present in IKEv1. Also, IKEv2 is an excellent choice for mobile users due to its MOBIKE support which allows IKEv2 connections to resist network changes.
Still, we do recommend choosing a VPN provider that offers access to multiple protocols alongside IKEv2. While it is a great option for mobile users, it doesn’t hurt to have even better protocols (like OpenVPN and SoftEther) as an alternative for other devices.
“WireGuard” is a registered trademark of Jason A. Donenfeld.
 What Is SoftEther? (Complete Guide)
What Is SoftEther? (Complete Guide)
 What Is IPSec and How Does it Work?
What Is IPSec and How Does it Work?
