The Top 8 VPN Security Risks (What to Look Out for)

VPNs are a great way to protect your Internet traffic and privacy from government surveillance, ISP snooping, and nosy hackers.
But did you know you can also expose yourself to VPN security risks if you’re not careful?
Here’s all you need to know about that.
“Wait – Aren’t VPNs Secure?”
Well, that depends.
If you pick the right provider, you’ll definitely get to enjoy great security and privacy.
The problem with that is finding said provider. There are hundreds of options on the market, and many VPN services actually endanger your data.
That’s exactly why we decided to write up an overview of the biggest VPN security risks, and showcase what red flags you need to look out for.
The Main 8 VPN Security Risks to Watch Out for
Here are the kinds of dangers you might expose yourself to if you pick a VPN provider that’s not big on privacy and security:
1. Logging Policies
Using a VPN to hide your browsing activities becomes pretty pointless if the provider is now the one who logs them instead of your ISP.
Unfortunately, that’s what happens when you pick a provider who keeps logs. You become exposed to severe VPN security risks simply because you no longer have control over your privacy.
Usage logs are the most dangerous ones since they track information about what you do on the web while using a VPN.
Connection logs are a bit more “innocent” since it’s just data about the connection itself, not what you do with the VPN. However, they’re still not okay since they violate your privacy. Not to mention the providers who use them are usually the ones who impose bandwidth limits.
A zero-log policy is the best one to go with if you really want to enjoy online freedom and privacy, and not have to worry about the dangers of VPN logging.
Also, VPNs that don’t support cryptocurrency payments are risky too.
Why?
Because they sometimes might need to log some personal information when you pay for their services with a credit card or a platform like PayPal. With cryptocurrencies, they don’t need any of it.
2. Data Leaks
A data leak is when you’re using a VPN to hide your traffic and IP address, but they still leak through the VPN tunnel. IP leaks, DNS leaks, and WebRTC leaks are all good examples of that. If they occur, they pretty much make using a VPN pointless.
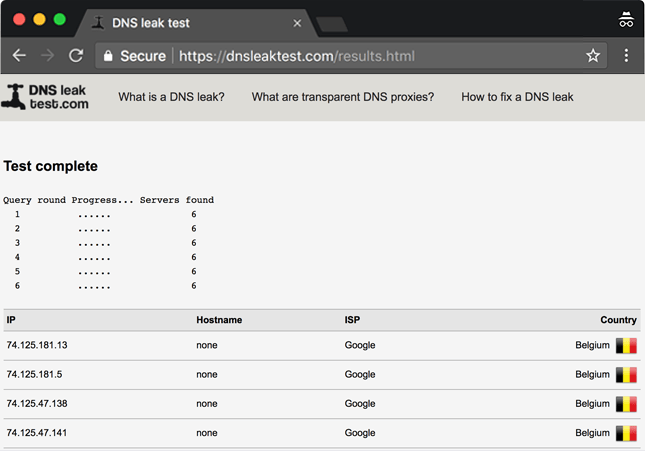
Now, these kinds of leaks can take place because the VPN provider didn’t configure their connections well. But they can also happen due to browser-related issues.
A decent provider will have safeguards in place to keep you from having your data exposed if something like this occurs.
If you want to test a VPN connection for leaks, feel free to use our guide.
3. Shady Privacy Policies
The devil is in the details.
A VPN provider can claim they respect your privacy and offer top-notch security in their marketing copy, while their Privacy Policy tells a completely different story. Usually, that’s where you’ll clearly find out if the provider also keeps any logs or not.
And depending on the wording in a provider’s Privacy Policy, they might subtly and vaguely mention they collect user data and share it with third parties (AKA advertisers). Free VPNs are the services that usually do this.
Why?
To make money, of course. Advertisers will pay handsomely to get their hands on your data, which they will use to create personalized profiles so that they can spam you with targeted ads.
What’s more, some providers might even display said targeted ads through their VPN clients.
While that might sound like just a minor inconvenience for some of you, think of it this way – what’s the point in using a VPN service to hide your traffic and data if the provider will just sell it to advertisers?
Don’t forget – the advertisers who buy your data won’t keep it to themselves. If they can make a profit, they’ll sell it to other third parties. If they don’t even bother doing a background check, some cybercriminal or scammer might end up getting their hands on your personal information.
All in all, a long, vague, and hard to understand Privacy Policy is a red flag.
4. Poorly-Configured Encryption
If the VPN provider didn’t do their homework, they might have made serious mistakes when configuring the encryption the VPN will use. In fact, free VPNs are very likely to have faulty encryption.
What does that mean for you?
That cybercriminals and surveillance agencies might actually manage to intercept your web traffic, and decrypt it by exploiting or brute-forcing the weak encryption.
A reliable VPN provider won’t have any problem sharing encryption details with their users.
5. Malware Infections
If you’re not careful enough, you might end up dealing with serious VPN risks – like malware being injected into your device when you download a VPN client, which will start spying on your activities, spamming you with malicious ads, and stealing your personal and financial details.
If you’re extremely unlucky, you might expose your device to ransomware which will encrypt your data, and ask for a big ransom in exchange for it.
This isn’t something new, unfortunately. A lot of free VPN services on the Google Play Store were actually found to be extremely malicious back in 2017.
6. Being Forced to Use PPTP
The PPTP protocol might be fast and convenient, but it’s extremely dangerous to use if you value your privacy.
Why?
Well, because the NSA already managed to decrypt PPTP traffic some time ago. And cybercriminals know that, so they’re more likely to target PPTP traffic when they’re looking for victims.
So, a VPN provider that only offers PPTP connections is a very risky choice.
Even if they offer L2TP/IPSec alongside it, things still don’t look good. While L2TP/IPSec is pretty secure, Snowden has claimed the protocol was deliberately weakened. How much you believe that is up to you, but keep in mind Microsoft co-developed L2TP with Cisco, and Microsoft was the first member of the PRISM surveillance program.
Ideally, a VPN provider should allow you to use stronger and safer protocols like IKEv2, OpenVPN, and SoftEther on top of protocols like PPTP or L2TP/IPSec.
7. The Provider Using Your IP Address as an Exit Node
What does that mean?
Basically, it’s when a VPN provider runs their network off of users’ bandwidth and IP addresses. The users “volunteer” their bandwidth and IP address for that, but many don’t realize they’re doing it since they don’t read the provider’s ToS and Privacy Policy.
Having your IP address used as an exit node is dangerous because it pretty much means other VPN users will be using it when they’re on the web.
So, a cybercriminal or scammer could do illegal stuff on the Internet while using your IP address – like downloading illegal torrents, DoS/DDoS-ing websites and networks, or sharing child pornography.
It’s not hard to imagine how that could land you in legal trouble.
That mostly sounds like speculation. Surely, VPN providers don’t do stuff like that, right?
Well, not all providers, but it does happen from time to time. A popular free VPN provider was actually caught turning users’ devices into exit nodes, and selling their bandwidth to third parties too.
8. No Extra Security Features
While a VPN with good encryption and a favorable no-log policy is great, a service that offers even more security features is even better. We’re talking about stuff like:
- DNS leak protection – Even if you test out the connections and don’t see any DNS leaks, it never hurts to know the VPN provider has measures in place that will prevent a DNS leak from taking you by surprise.
- Internet Kill Switches – This type of Kill Switch is vital for protecting your privacy. Basically, if your VPN connection ever goes down, your web traffic will stop. It will only resume when the VPN is running well again.
- Application-level Kill Switches – Offers you a good way to control which applications can’t use the web when your VPN connection is down. Very useful for torrent and email apps.
Now, we’re not saying a VPN provider who doesn’t offer features like that isn’t trustworthy. But you’ll definitely get some nice peace of mind knowing the provider went the extra mile to make sure your privacy will be safe and sound – even if something goes wrong on their end by accident.
Can’t the Country a Provider Is Based in Be a Concern?
Not necessarily. While you might hear people saying it’s not a good idea to pick a VPN provider who has their HQ or servers in Five/Nine/Fourteen Eyes countries, your privacy will only be in danger if said VPN keeps any logs about your activities.
If they have a zero-log policy, you’ve got nothing to worry about. Even if a country’s government would use laws to force to provider to hand over user data, they wouldn’t have any information they can share to begin with.
Of course, if the provider keeps logs, you’ve got something to worry about. Your best bet is to switch to a service that doesn’t.
How to Avoid VPN Security Issues
Obviously, the best way to do that is to make sure the provider was never involved in any privacy or security scandals, check dozens of reviews to see what other people have to say about them, and make sure they meet the security standards we outlined in this article (secure VPN protocols, good security features, no-logging policies, etc.)
Also, you can try using our guide (the one we mentioned above) to see if there are any issues with the VPN you’re using.
Oh, and one of the easiest ways to avoid VPN security risks is to not use free VPN services. Free providers are usually the ones who sell your data to advertisers, expose you to malware, steal and sell your bandwidth, and spam you with annoying ads.
After all, they gotta make money somehow if they’re not charging you for their service.
Need a Secure VPN?
CactusVPN is gonna be right up your alley.
We offer a VPN service that offer military-grade encryption, and a choice between six VPN protocols: OpenVPN, SoftEther, IKEv2, SSTP, PPTP, L2TP/IPSec.
What’s more, we provide access to an Internet Kill Switch, an application-level Kill Switch, and DNS leak protection. Also, we don’t keep any logs.
That, and we support cryptocurrency payments for our subscriptions if you’re looking to retain as much anonymity as possible when buying a VPN service.
Oh, and our support team works 24/7, so you can always rely on us for help if you encounter any issues.
Special Deal! Get CactusVPN for $3.5/mo!
And once you do become a CactusVPN customer, we’ll still have your back with a 30-day money-back guarantee.
Conclusion
VPNs are generally safe enough to use, but not all providers go the extra mile to make sure their services 100% protect users’ privacy.
If you are unlucky enough to deal with such a provider, you expose yourself to VPN security risks like:
- Having your data sold to advertisers.
- Having your privacy violated by logs.
- Malware infections and poorly-configured encryption.
- IP, DNS, and WebRTC leaks.
- Having your IP address used as an exit node.
- Lack of security features and strong protocols.
So make sure you pick a VPN provider that is reliable, offers high-security features, and has a transparent Privacy Policy.